Практически. БКС практические. Перечень лабораторных работ
 Скачать 1.44 Mb. Скачать 1.44 Mb.
|
ЛАБОРАТОРНАЯ РАБОТА № 23“ Настройка IPSec на Cisco ASA.”(2 часа) ПМ.03 «Эксплуатация объектов сетевой инфраструктуры» МДК.03.02 Безопасность компьютерных сетей Составители(авторы) ВилковА.Н. преподаватель ФГБОУ ВО "РЭУ им. Г.В.Плеханова" 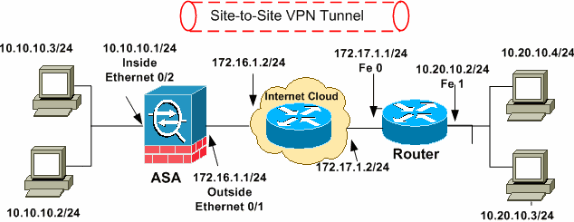 Топология сети Ход работы: Настройка Cisco ASA !--- Configure the outside interface. ! interface Ethernet0/1 nameif outside security-level 0 ip address 172.16.1.1 255.255.255.0 !--- Configure the inside interface. ! interface Ethernet0/2 nameif inside security-level 100 ip address 10.10.10.1 255.255.255.0 !-- Output suppressed ! passwd 2KFQnbNIdI.2KYOU encrypted ftp mode passive dns server-group DefaultDNS domain-name default.domain.invalid access-list 100 extended permit ip any any access-list inside_nat0_outbound extended permit ip 10.10.10.0 255.255.255.0 10.20.10.0 255.255.255.0 !--- This access list (inside_nat0_outbound) is used !--- with the nat zero command. This prevents traffic which !--- matches the access list from undergoing network address translation (NAT). !--- The traffic specified by this ACL is traffic that is to be encrypted and !--- sent across the VPN tunnel. This ACL is intentionally !--- the same as (outside_1_cryptomap). !--- Two separate access lists should always be used in this configuration. access-list outside_1_cryptomap extended permit ip 10.10.10.0 255.255.255.0 10.20.10.0 255.255.255.0 !--- This access list (outside_cryptomap) is used !--- with the crypto map outside_map !--- to determine which traffic should be encrypted and sent !--- across the tunnel. !--- This ACL is intentionally the same as (inside_nat0_outbound). !--- Two separate access lists should always be used in this configuration. pager lines 24 mtu inside 1500 mtu outside 1500 no failover asdm image disk0:/asdm-613.bin asdm history enable arp timeout 14400 global (outside) 1 interface nat (inside) 1 10.10.10.0 255.255.255.0 nat (inside) 0 access-list inside_nat0_outbound !--- NAT 0 prevents NAT for networks specified in !--- the ACL inside_nat0_outbound. access-group 100 in interface outside route outside 0.0.0.0 0.0.0.0 172.16.1.2 1 timeout xlate 3:00:00 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 timeout mgcp-pat 0:05:00 sip 0:30:00 sip_media 0:02:00 timeout uauth 0:05:00 absolute http server enable http 0.0.0.0 0.0.0.0 dmz no snmp-server location no snmp-server contact !--- PHASE 2 CONFIGURATION ---! !--- The encryption types for Phase 2 are defined here. crypto ipsec transform-set ESP-DES-SHA esp-des esp-sha-hmac !--- Define the transform set for Phase 2. crypto map outside_map 1 match address outside_1_cryptomap !--- Define which traffic should be sent to the IPsec peer. crypto map outside_map 1 set peer 172.17.1.1 !--- Sets the IPsec peer crypto map outside_map 1 set transform-set ESP-DES-SHA !--- Sets the IPsec transform set "ESP-AES-256-SHA" !--- to be used with the crypto map entry "outside_map". crypto map outside_map interface outside !--- Specifies the interface to be used with !--- the settings defined in this configuration. !--- PHASE 1 CONFIGURATION ---! !--- This configuration uses isakmp policy 10. !--- The configuration commands here define the Phase !--- 1 policy parameters that are used. crypto isakmp enable outside crypto isakmp policy 10 authentication pre-share encryption des hash sha group 1 lifetime 86400 telnet timeout 5 ssh timeout 5 console timeout 0 threat-detection basic-threat threat-detection statistics access-list ! tunnel-group 172.17.1.1 type ipsec-l2l !--- In order to create and manage the database of connection-specific !--- records for ipsec-l2l— IPsec (LAN-to-LAN) tunnels, use the command !--- tunnel-group in global configuration mode. !--- For L2L connections the name of the tunnel group MUST be the IP !--- address of the IPsec peer. tunnel-group 172.17.1.1 ipsec-attributes pre-shared-key * !--- Enter the pre-shared-key in order to configure the !--- authentication method. telnet timeout 5 ssh timeout 5 console timeout 0 threat-detection basic-threat threat-detection statistics access-list ! class-map inspection_default match default-inspection-traffic Настройка маршрутизатора: !--- Configuration for IKE policies. !--- Enables the IKE policy configuration (config-isakmp) !--- command mode, where you can specify the parameters that !--- are used during an IKE negotiation. Encryption and Policy details are hidden as the default values are chosen. crypto isakmp policy 2 authentication pre-share !--- Specifies the pre-shared key "cisco123" which should !--- be identical at both peers. This is a global !--- configuration mode command. crypto isakmp key cisco123 address 172.16.1.1 ! ! !--- Configuration for IPsec policies. !--- Enables the crypto transform configuration mode, !--- where you can specify the transform sets that are used !--- during an IPsec negotiation. crypto ipsec transform-set ASA-IPSEC esp-des esp-sha-hmac ! !--- !--- Indicates that IKE is used to establish !--- the IPsec Security Association for protecting the !--- traffic specified by this crypto map entry. crypto map SDM_CMAP_1 1 ipsec-isakmp description Tunnel to172.16.1.1 !--- !--- Sets the IP address of the remote end. set peer 172.16.1.1 !--- !--- Configures IPsec to use the transform-set !--- "ASA-IPSEC" defined earlier in this configuration. set transform-set ASA-IPSEC !--- !--- Specifies the interesting traffic to be encrypted. match address 100 ! ! ! !--- Configures the interface to use the !--- crypto map "SDM_CMAP_1" for IPsec. interface FastEthernet0 ip address 172.17.1.1 255.255.255.0 duplex auto speed auto crypto map SDM_CMAP_1 ! interface FastEthernet1 ip address 10.20.10.2 255.255.255.0 duplex auto speed auto ! interface FastEthernet2 no ip address ! interface Vlan1 ip address 10.77.241.109 255.255.255.192 ! ip classless ip route 10.10.10.0 255.255.255.0 172.17.1.2 ip route 10.77.233.0 255.255.255.0 10.77.241.65 ip route 172.16.1.0 255.255.255.0 172.17.1.2 ! ! ip nat inside source route-map nonat interface FastEthernet0 overload ! ip http server ip http authentication local ip http secure-server ! !--- Configure the access-lists and map them to the Crypto map configured. access-list 100 remark SDM_ACL Category=4 access-list 100 remark IPSec Rule access-list 100 permit ip 10.20.10.0 0.0.0.255 10.10.10.0 0.0.0.255 ! ! ! !--- This ACL 110 identifies the traffic flows using route map access-list 110 deny ip 10.20.10.0 0.0.0.255 10.10.10.0 0.0.0.255 access-list 110 permit ip 10.20.10.0 0.0.0.255 any route-map nonat permit 10 match ip address 110 ! control-plane ! ! line con 0 login local line aux 0 line vty 0 4 privilege level 15 login local transport input telnet ssh Контрольные вопросы: Описание технологии IPSec Описание виртуальной частной сети |
